Friend Spam
From Dark Patterns
Contents |
Definition
A site or game asks for your twitter or email credentials (either via the password antipattern or via OAuth for an allegedly benign purpose (e.g. finding friends who are already using that service), but then goes on publish content or send out bulk messages using your account - i.e. from you. This is technique is commonly used by viruses - but even well-known companies sometimes engage in "friend spam".
Example: Twifficiency app promotion spam (August 2010)
Twifficiency is a perfect example of the friend spam dark pattern put into action on Twitter using OAuth. However, we should give the developer, James Cunningham, a break, as it was simply a small personal side project that took off in a huge way before he had a chance to properly evaluate the impact of his design decisions.
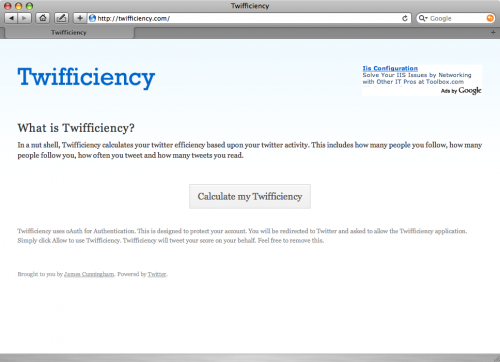
The Twifficiency.com homepage is visually designed to come across as clean, simple and credible. In small print at the bottom of the page, some text states that "Twifficiency will tweet your score on your behalf. Do not use this app if you do not consent to this.". However, this text is tiny and since most users scan-read on the web, many people did not notice it.
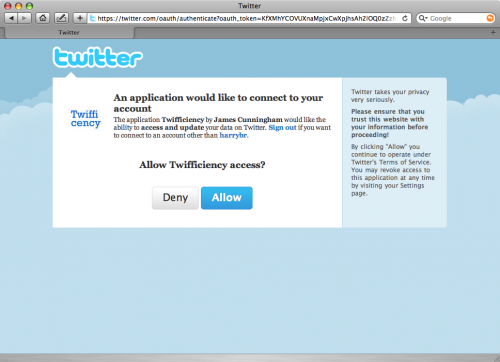
As you can see above, this Twitter.com OAuth page doesn't emphasise the point that you are granting the app the ability to tweet on your behalf, rather than simply to index your public tweets. This is clearly a design mistake. In this respect, we can blame Twitter for the volume of tweeted friend spam that is currently occurring from apps.
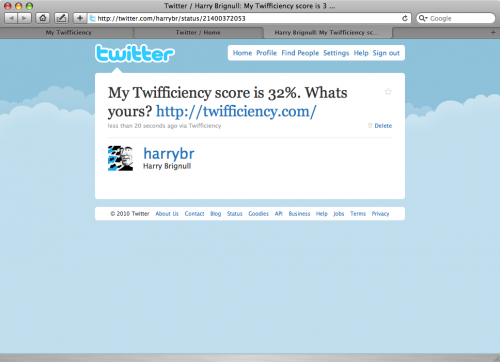
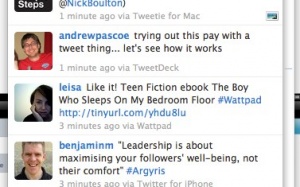
Here's an example of the friend spam tweeted by Twifficiency. Using someone's voice as a means to convince their friends to take an action is very effective because it takes advantage of human cognitive biases such as Social Proof, Authority and Liking.
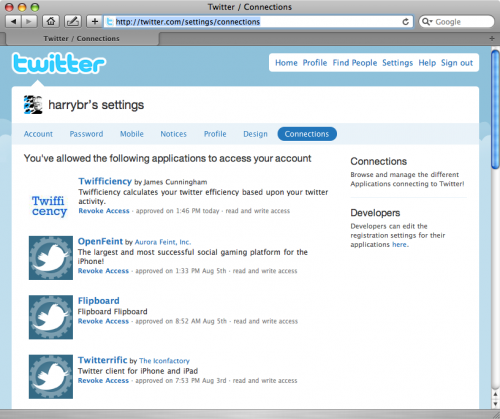
Twifficiency sets itself up with permanent access to your twitter account using OAuth. This fact in particular has made some pundits particularly concerned. Twitter needs to reconsider how well they communicate the implications of permanent access in the OAuth user journey.
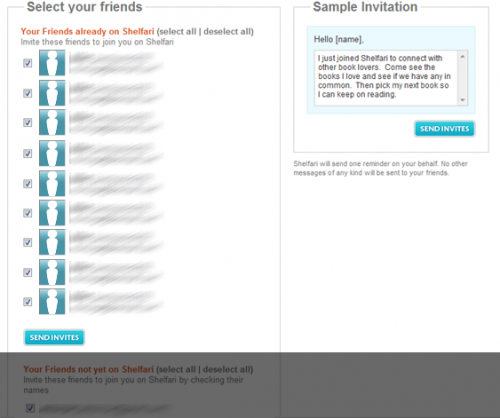
Example: Shelfari invitation spam (2007)
Shelfari claim this was nothing but a design mistake, whereby they mistakenly placed an opt-out checkbox below the fold. This is shown in the screengrab below (greyed area depicts the fold):
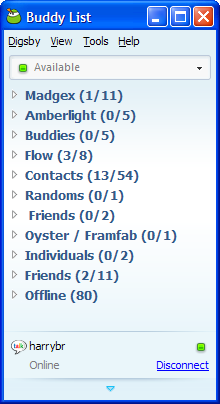
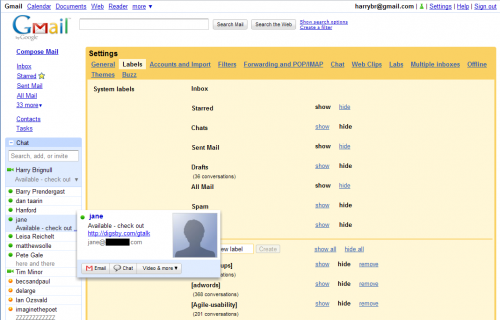
Example: Digsby Instant Messenger Client (2010)
Digsby secretly appends a text ad on the end of your instant messenger status message.
When you install and run Digsby, it gives no indication that it will manipulate your IM status message. As you can see here, my status is simply shown as "Available". If you refer to the image below, you'll see what Digsby appends to your status message, as seen by other users (in the example, Jane is using Digsby).
Example: Goodreads Twitter sign-up journey (September 2010)
Goodreads.com is currently running a sign-up user journey that involves the Friend Spam dark pattern. First, a twitter user notices that a friend has tweeted something along the lines of "Check out my shelves on Goodreads: http://xxx.ly/xxxxx". When the user clicks this, they are invited to give Goodreads.com twitter authorisation. Having done that, the user is shown an "add friends" page (shown below). There is a preselected checkbox at the bottom labelled "Share goodreads with my Twitter friends that don't have an account yet". If the user forgets to untick this checkbox, Goodreads automatically sends out a tweet using your account credentials. It does this "secretly" - the only way a user will notice is by checking their own twitter feed.

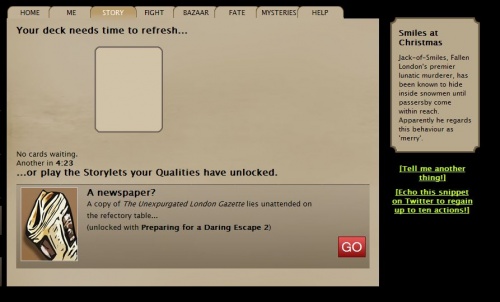
Example: Echo Bazaar (2009-2011)
The game requires Facebook or Twitter OAuth to play. Initially, when a player first joined the game, on the sign-up screen, the "Echo this message on your social network, once only:" tickbox was automatically checked. (If the player didn't uncheck it, the site advertised itself on their Facebook or Twitter page.) This was later changed, apparently in late 2010, so that the box started unticked.
In the game itself, players are given seventy actions per day, which are spent by performing the core activities of the game. Players are given the option to increase that to eighty actions per day if they are willing to post an advert for Echo Bazaar to their Twitter/Facebook stream every single day. By default, the message is a cryptic phrase from the game itself, but the player is allowed to edit the ad message however they wish, so long as they URL is intact. This ad can only be posted once per day.
A new player only starts the game with ten actions; when those have been used up, the player has to choose between waiting for those actions to refill (which would take 70 minutes), or clicking a button to post an Echo Bazaar ad to their Twitter stream, which would refill their actions immediately.
It's not uncommon to see players simply working the URL into their day-to-day Twitter postings by using the edited message to make a normal, but truncated tweet. Players seem relatively comfortable with the idea of spamming their friends with a URL advert once per day, in return for a benefit given to them inside the game - the advantage of a whole ten extra actions in the game universe (which will let you level up more quickly than a player who refuses to advertise on Twitter) seems greater than the drawback of very slightly annoying a number of Twitter friends.
Echo Bazaar appear to accept that this form of Twitter advertising annoys people, but "want to limit that annoyance to, oh, the kind of annoyance I'll feel when the World Cup rolls round and half my friends start tweeting about bloody football".
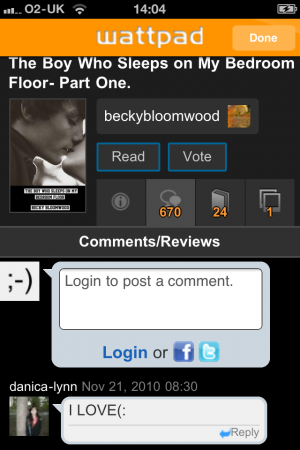
Example: Wattpad (2010)
This iPhone application - an ebook reader that allows 'readers and writers to discover, share and connect' allows you to log in using Twitter OAuth and creates a profile that takes your photo, byline, and location from your twitter account.
Within the 'Info' screen of any book/story that you are reading there is a 'vote' button. There is little indication as to what 'vote' means (can you vote for or against, for example), and on selecting the 'vote' button the user is informed that their vote has been registered.
It is only when the reader returns to their twitter stream that they may then discover that they have unwittingly broadcast to their Twitter followers that they LIKE the ebook that they have voted for,
and many then hastily issue a retraction.